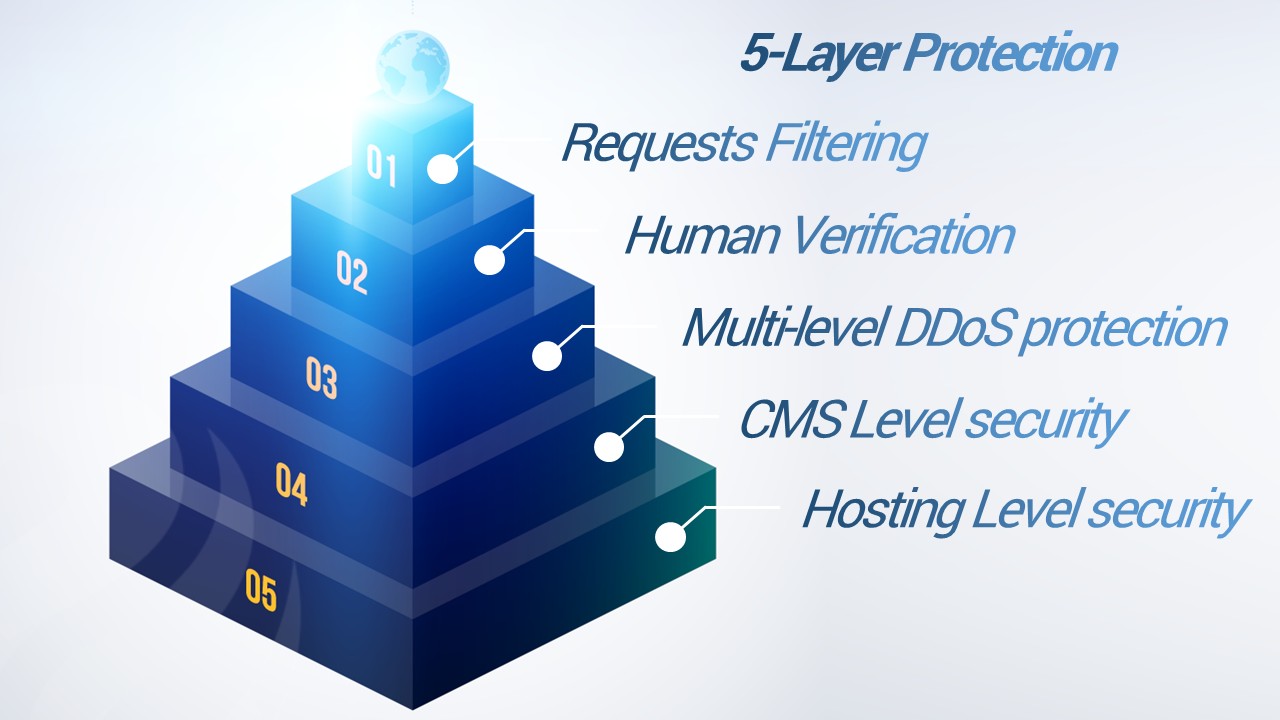
What do LinkedIn, Ashley Madison, Yahoo! and Target have in common? These companies have suffered large-scale data breaches. The aim of this article is to look at website security, how it relates to WordPress platforms in particular, and how you can be proactive in preventing and reducing the chances of falling victim to a cyber attack. Be sure to check out our guide to website security for tips and advice on how to set up and build strong passwords and boost your website security and online presence.
Website Security and Your Content Management System (CMS)
In the past few years, there has been a proliferation of great tools and services in web development. CMS platforms like WordPress, Joomla, and Drupal allow business owners to quickly and efficiently build an online presence.
These popular CMS platforms are battle-hardened, thanks to their widespread adoption, and have defined processes to handle vulnerabilities. These are well documented on their home pages.
Combined with their highly extensible architectures, rich plugins, modules and extension ecosystems, these platforms have made it easier than ever to get a website up and running without years of training.
WordPress is the most popular content management system available. Currently, it’s powering approximately 28% of the entire WebSphere and can be used well by both new and experienced developers. More importantly, it can also be used poorly. Among those in the web developer community, however, WordPress has a reputation as being less secure when compared to other solutions. Even with built-in securities, there is an unfortunate side effect to the growing popularity and use of these platforms in that now there are many users building an online presence who do not fully understand the risks, how to make sure their website is secure, or even understand the importance of securing their website.
This isn’t another top ten list of ultimate security tips for guaranteeing your site is safe from attack. Those articles typically contain a checklist of mostly ineffective suggestions and techniques which do nothing other than provide a false sense of security.
Instead, I’d like to focus on what really matters – the fundamentals – which are often overlooked. This is not a “how-to” but rather a suggestion of what to be aware of.

1. Update, Update, Update! Seriously, do the updates!
51% of sites were hacked via a security issue in a theme or plugin being used on their website.
This is something that cannot be stressed enough! Countless websites are compromised every day due to outdated and insecure software. It’s important to keep your website updated as new versions of a plugin or CMS version becomes available.
As I mentioned previously, most hacking is done through entirely automated means. Bots are constantly scanning websites for any opportunity. It is not good enough to update once a month, as bots are very likely to find any vulnerability before it can be patched.
If you’re running WordPress, Drupal, Joomla or even a simple HTML website, you should consider following @sucuri_security on Twitter to get notified about important updates and website security warnings.

2. The Importance of Strong Passwords
8% of websites were hacked because of weak passwords.
As the Interactive Director for Davidson Belluso, when doing website work, both on our own site, as well as on the websites of our clients, I often need to log into the backend of the site/server using the admin user credentials. I am frequently amazed and disturbed by how insecure some passwords are.
If your password appears in this list of most common passwords, it is pretty much guaranteed that your website will be hacked. Even if your password is not on this list, there are a lot of misconceptions about “strong” passwords. The lax requirements on most password strength meters are part of the problem.
When it comes to choosing a password there are three key requirements that should always be followed. For tips and advice on how to set up and build strong passwords, check out our guide at the beginning of this article.
3. One Website = One Container
41% of all websites are hacked through a security vulnerability on their hosting platform.
So you have an “unlimited” web hosting plan and figure why not host all of my sites on a single server? In addition to being sloppy, this is one of the worst website security practices I’ve seen and is a common mistake that prioritizes convenience over security.
Hosting many sites in the same location creates a very large attack surface. Not only can this result in all your websites being hacked at the same time, but it also makes the cleanup process a great deal more time-consuming, difficult, and expensive.
4. Sensible User Access
It’s important that every user has the appropriate permissions they require to do their job. If they require escalated permissions momentarily, grant it, then reduce it once the job is complete. This is a concept known as Least Privileged and is a frequently overlooked part of user management: accountability and monitoring.
This will reduce the fallout of compromised accounts and can protect against the damage done by a ‘rogue’ user. If people share a user account and unwanted changes are made by that user, how do you find out which person on your team was responsible?
With a separate account for each user, you can keep an eye on user behavior by reviewing logs and knowing the usual behavior (when and where they normally access the website) so you can spot anomalies and confirm with the person that their account hasn’t been compromised.
Watching logs is one of the basics of website management – what are users doing? And where are they coming from? If you see one of your employees logging from an IP address that traces back to the Balkans, there may be a chance that something isn’t right.
5. Change the Default CMS Settings!
Most CMS applications have default settings that make them easy to use. From a website security perspective, this should be adjusted. As I’ve mentioned, the most common attacks against websites are entirely automated. Many of these attacks rely on the default settings being used. This means that you can avoid a large number of attacks simply by changing the default settings when installing the CMS of your choice.
For example, some CMS applications are writeable by the user, allowing a user to install whatever extensions they want. There are settings that you may want to adjust to control comments, users, and the visibility of your user information. The file permissions are another example of a default setting that can be hardened. It is usually easiest to change these default settings when initially installing your CMS, but they can be revisited and changed later.
6. Plugins, Modules and Extensions
One of the great things about current CMSs is their extensibility. What most don’t realize, however, is that that same extensibility can also be their biggest weakness. There are a massive number of plugins, add-ons, and extensions providing virtually any functionality you can imagine. However, the reality is that a massive number of extensions can be a double-edged sword. Often there are multiple extensions offering similar functionality. How do you know which one to install?
One of the first things I look for is how current the latest version of the extension is, and when it was last updated. If the last update was more than a year ago, my concern is that the author has stopped working on it. I much prefer to use extensions that are actively being developed, because it indicates that the author would at least be willing to implement a fix in the event that any security issues are discovered or reported. If an extension is not supported by the author, it may not be the best solution for your website as it may stop working at any time.
I also look at the age of an extension, the number of installs, and the rating. I read the support forums and other developer comments and how they rated it. Also important is if the plugin was developed by an established author with numerous installs, as this indicates a more trustworthy source than one that has a few installs or was recently released by a first-time developer. Not only is the experienced developer much more likely to have a good idea about best website security practices, but they are far less likely to damage their reputation by inserting malicious code into their extension.
I can’t stress how important it is that you download all of your extensions and themes from legitimate sources. There are sites that offer ‘free’ versions that are normally premium and require payment to download. These ‘free’ versions are pirated and frequently infected with malware, and are typically set up with only one goal: to infect as many websites as possible.
7. Backups
Making backups of your website is very important. Not having a backup when you need it will only compound a catastrophic event. It is never safe to assume that someone else will take care of it. At the very least, you need to initiate the script or protocol to do this daily or weekly. You will be very thankful if you take the time to consider the best website backup solutions for your website.
8. Server Configuration Files
You should really get to know your web server configuration and which file formats are used:
- Apache web servers use the .htaccess file
- Nginx servers use nginx.conf
- Microsoft IIS servers use web.config
Most often found in the root web directory, these files are very powerful as they allow you to execute server rules, including directives, that improve your website security and performance.
If you aren’t sure which web server you use, you can run your website through Sitecheck and click the Website Details tab.
There are many rules and options that can be considered for a secure web server configuration file, but at a minimum, you should take the following steps:
- Prevent directory browsing
- Prevent image hotlinking
- Protect sensitive files
9. Install an SSL
An SSL encrypts communications between Point A and Point B – the website server and browser. Though it won’t protect your website against malicious attacks or stop it from distributing malware if/once hacked, this encryption is important for one specific reason: it prevents anyone from being able to intercept that communication and traffic. This is known as a Man in the Middle (MITM) attack.
SSL is especially important for E-Commerce website security, and any website that accepts form submissions with sensitive user data or Personally Identifiable Information (PII), and it protects your visitor’s information in transit, which in turn protects you from incurring any fines that come along with being found noncompliant with PCI DSS.
10. Finally…
Securing your website is something you need to take seriously. If you don’t take any security precautions for your website, you will be hacked eventually. Guaranteed.
Every business should have a professional in charge of updating, maintaining, and protecting its website. This individual or team should have knowledge of how a website, server, and hosting operates. This includes constantly updating your core CMS system, plugins, and any other third-party integrations running on your site.
It just so happens, being one such professional, I can recommend a team specifically dedicated to keeping your website safe, secure, and up-to-date every day.